Let’s go back to our Quantum Technology Series! Last time, we explored the One-Time Pad (read here), one of the simplest and strongest encryption schemes ever devised. Our long-term goal is to understand how today’s internet security protocols work — but before we can get there, we need to grasp one small but powerful mathematical idea: modular arithmetic.
Usually, we think of numbers stretched out in a straight line, with negatives on the left, positives on the right, and zero in the middle. But not everything in life runs in a straight line. Some things move in cycles. Time, for instance, loops every 12 hours on a clock. After 12 comes 1 again, and after 24 hours the Earth completes one full rotation, returning to the same point where it began. This kind of repeating pattern is called periodic, and the time it takes to return to the beginning is called its period.
Music behaves in a similar way. There are only 12 notes in the standard Western musical scale, each with a frequency related to the others. When you double the frequency, say from 440 Hz to 880 Hz, the sound feels the same—an octave higher, but still the same note. That’s because of how our ears and brain work: we don’t hear those two sounds as completely different, but as the same note repeating on a higher level. In a way, our sense of pitch naturally repeats—once we reach the top, it loops back to the start.

To describe such repeating systems, mathematicians came up with a clever idea called modular arithmetic. Instead of laying numbers out on a line, we imagine them arranged in a circle, like a clock. The size of that circle is called the modulus, often shortened to mod.
Let’s build this kind of math ourselves.
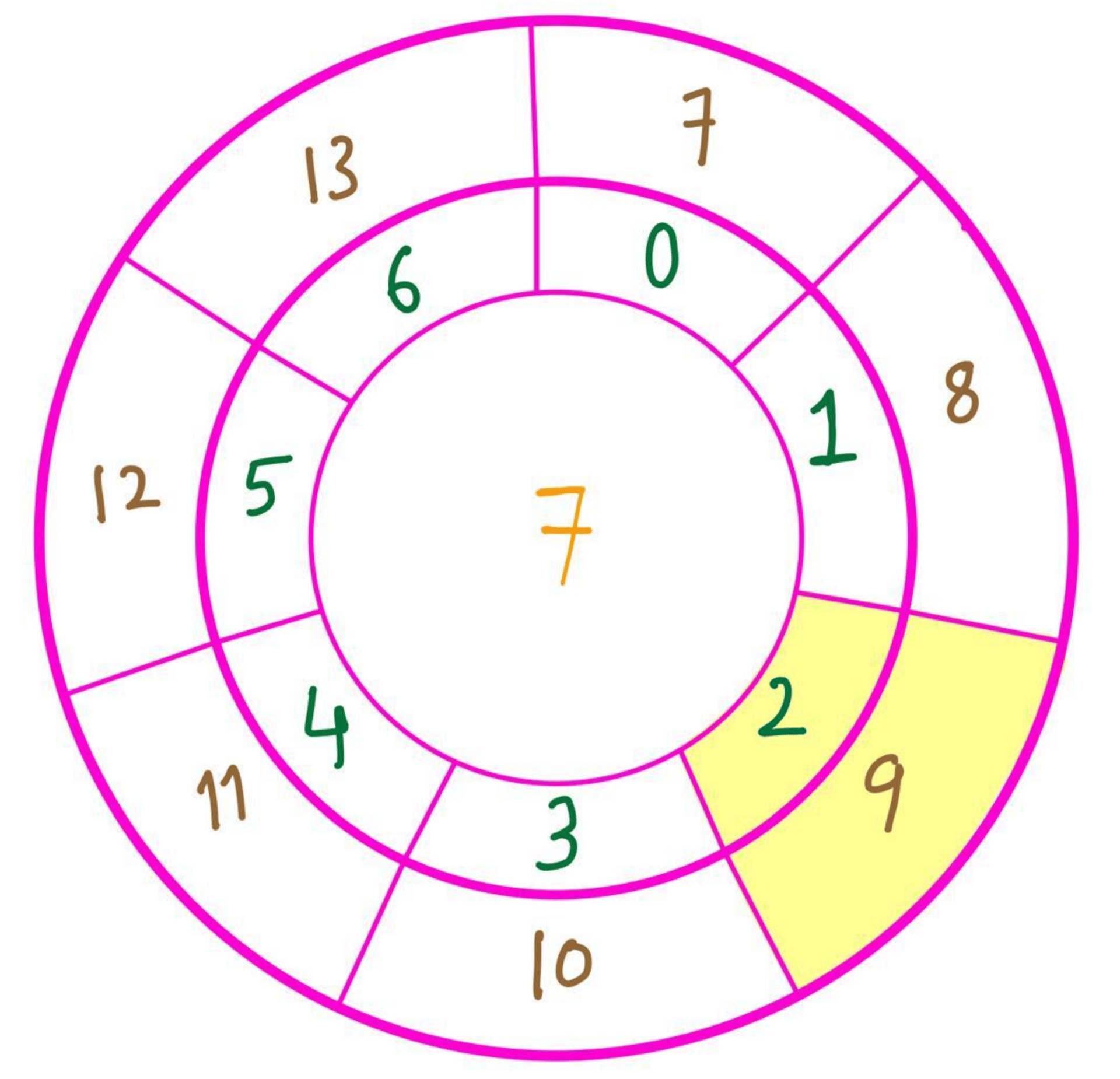
Step 1: Pick any number you like. Let’s say 7. This number defines the period of our circle, the modulus.
Step 2: Ask yourself: what are the possible remainders when a number is divided by 7? Those are precisely the numbers that go on the circle. For 7, the possible remainders are {0, 1, 2, 3, 4, 5, 6}.
Step 3 (Optional): Draw the circle with those numbers.

That’s all it takes! But there are three key ideas to keep in mind:
We can group every integer into “baskets,” where each basket holds all numbers that leave the same remainder when divided by 7. For example, 9, 16, and 23 all leave a remainder of 2 when divided by 7, so they belong to the same basket.
All numbers in the same basket are considered equal (yellow region in the figure below)—but equal only in the world of modular arithmetic. Mathematicians use the word congruent instead of equal, written with the symbol “≡.”
So, in mod 7 arithmetic, we can say that 9 is congruent to 16, and we write it like this:
16 ≡ 9 (mod 7).
In this circular world, equality takes on a new shape—it bends back on itself, looping around every 7 steps.
Real life Applications:
What makes this so powerful is how often such circular reasoning shows up in real life. One of the earliest uses of modular arithmetic was in cryptography. Julius Caesar is said to have encoded his military messages by shifting each letter in the alphabet by a fixed number of steps. If you shift every letter by three places, A becomes D, K becomes N, and Y becomes B. After Z, the alphabet simply wraps back to A again. This is arithmetic modulo 26, since there are 26 letters. If you shift by 26, everything stays the same; shifting by 27 is just like shifting by one. Try decoding this message: KHOOR ZRUOG!

Even today, modular arithmetic protects us in ways we barely notice. Before barcode scanners, librarians had to type book numbers—the ISBNs—by hand, and typing mistakes were common. To catch these errors, the ISBN system includes a checksum, a small number computed using modular arithmetic. If even one digit is wrong, the final sum won’t fit the pattern, and the computer knows immediately that something went wrong. ISBN-13 uses mod 10.
So when you set your alarm, you might think, “It’s 11 PM now, and I’ll sleep for 8 hours, so 11 + 8 = 7.” You’re not joking or making a mistake—you’re just thinking in a circular world. Modular arithmetic gives us a way to describe repetition and cycles wherever they appear, from clocks and music to encryption and data integrity. It’s one of those quiet, elegant ideas that turn out to be everywhere once you start noticing them—always looping back on itself.
We now have everything we need to understand how modern internet security systems work. We'll explore that in the next episode, so stay tuned.
Post Script:
Thank you my readers! If you enjoyed the article, please do share it! I’d really appreciate your feedback to help make the content better as we go forward. Drop an email: [email protected]


